#Data Encryption Software
Explore tagged Tumblr posts
Text
How to Choose the Right Antivirus Software: A Comprehensive Guide
In today’s digital age, where our lives are intricately intertwined with technology, safeguarding our digital assets has become paramount. With the proliferation of cyber threats, antivirus software stands as a crucial line of defense against malware, viruses, ransomware, and other malicious entities lurking online. However, the abundance of antivirus options can be overwhelming, making it…

View On WordPress
#A#Advanced Behavioral Analysis Software#Advanced Threat Detection#Antivirus#Antivirus Software#Automated Security Incident Response#Cloud Security Solutions#Cloud-Based Endpoint Security Platform#Comprehensive Data Protection Suite#Continuous Vulnerability Assessment#Cyber Defense#Cybersecurity#Cybersecurity Awareness Training#Data Encryption Software#Data Protection#Defense#Encryption#Endpoint Protection Suite#Endpoint Security#Firewall#Firewall Protection#Identity Theft#Identity Theft Prevention#Integrated Firewall Protection Mechanism#Internet Security Software#Malware#Malware Detection#Malware Removal Tool#Mobile Device Management#Multi-Layered Malware Defense System
0 notes
Text
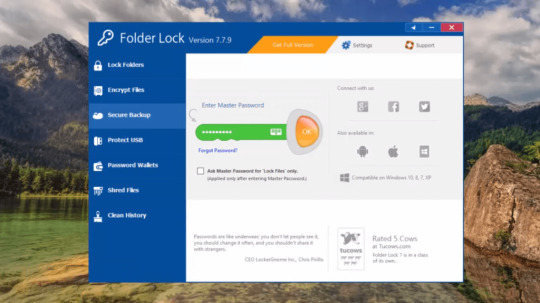
Folder Lock
If you have folders and files that you want to keep private, consider using Folder Lock. Unlike My Lockbox, it isn’t a free app, but it offers excellent configuration options and numerous methods to protect important and private documents from prying eyes. Folder Lock is a complete solution for keeping your personal files encrypted and locked, while automatically and in real-time backing up…
View On WordPress
#Data Encryption#Digital Wallets#Encryption Software#File Locking#File Management#File Security#File Shredding#password protection#Portable Security#privacy protection#Secure Backup#Windows Security
0 notes
Text
#best encryption tools#computer security#cybersecurity#data breach prevention#data encryption guide#data privacy#data protection#data safety#data security tips#digital security#encrypting personal information#encryption basics#encryption FAQs#encryption for beginners#encryption software#encryption solutions#encryption techniques#guide to data encryption#how to encrypt data#online privacy#personal data security#prevent cyber attacks#privacy software#protect data online#secure communication#secure data encryption#secure files and folders#secure personal data#software for encryption#strong encryption methods
1 note
·
View note
Text
How should we handle microservice data privacy compliance
Microservices handling sensitive user data are not compliant with data privacy regulations, risking legal consequences. Solution: Implement data anonymization and encryption techniques for sensitive information. Conduct regular compliance checks and audits to ensure adherence to privacy regulations. Terminology: Data Anonymization protects privacy by altering or removing personally…
View On WordPress
#Best Practices#Encryption#interview#interview questions#Interview Success Tips#Interview Tips#Java#Microservice Data Privacy Compliance#Microservices#Senior Developer#Software Architects
0 notes
Text
Securing Your Website: Best Practices for Web Developers
As the digital landscape continues to evolve, website security has become a paramount concern for businesses and individuals alike. With cyber threats becoming increasingly sophisticated, it is crucial for web developers to adopt robust security measures to safeguard their websites and the sensitive data they handle. In this article, we'll delve into the best practices that web developers can implement to enhance the security of their websites and protect against potential threats.
Introduction
In today's interconnected world, websites serve as the digital storefront for businesses, making them vulnerable targets for cyber attacks. From data breaches to malware infections, the consequences of a security breach can be severe, ranging from financial loss to damage to reputation. Therefore, prioritizing website security is essential for maintaining the trust and confidence of users.
Understanding Website Security
Before diving into best practices, it's crucial to understand the importance of website security and the common threats faced by websites. Website security encompasses measures taken to protect websites from cyber threats and unauthorized access. Common threats include malware infections, phishing attacks, SQL injection, cross-site scripting (XSS), and brute force attacks.
Best Practices for Web Developers
Keeping Software Updated
One of the most fundamental steps in website security is keeping all software, including the content management system (CMS), plugins, and server software, updated with the latest security patches and fixes. Outdated software is often targeted by attackers due to known vulnerabilities that can be exploited.
Implementing HTTPS
Implementing HTTPS (Hypertext Transfer Protocol Secure) encrypts the data transmitted between the website and its users, ensuring confidentiality and integrity. HTTPS not only protects sensitive information but also boosts trust among visitors, as indicated by the padlock icon in the browser's address bar.
Using Strong Authentication Methods
Implementing strong authentication methods, such as multi-factor authentication (MFA) and CAPTCHA, adds an extra layer of security to user accounts. MFA requires users to provide multiple forms of verification, such as a password and a one-time code sent to their mobile device, reducing the risk of unauthorized access.
Securing Against SQL Injection Attacks
SQL injection attacks occur when malicious actors exploit vulnerabilities in web applications to execute arbitrary SQL commands. Web developers can prevent SQL injection attacks by using parameterized queries and input validation to sanitize user inputs effectively.
Protecting Sensitive Data
It's essential to employ encryption techniques to protect sensitive data, such as passwords, credit card information, and personal details, stored on the website's servers. Encrypting data at rest and in transit mitigates the risk of data breaches and unauthorized access.
Regular Security Audits
Conducting regular security audits helps identify vulnerabilities and weaknesses in the website's infrastructure and codebase. Penetration testing, vulnerability scanning, and code reviews enable web developers to proactively address security issues before they are exploited by attackers.
Choosing a Secure Hosting Provider
Selecting a reputable and secure hosting provider is critical for ensuring the overall security of your website. When evaluating hosting providers, consider factors such as security features, reliability, scalability, and customer support.
Evaluating Security Features
Choose a hosting provider that offers robust security features, such as firewalls, intrusion detection systems (IDS), malware scanning, and DDoS protection. These features help protect your website from various cyber threats and ensure continuous uptime.
Ensuring Regular Backups
Regularly backing up your website's data is essential for mitigating the impact of security incidents, such as data breaches or website compromises. Choose a hosting provider that offers automated backup solutions and store backups securely offsite.
Customer Support and Response to Security Incidents
Opt for a hosting provider that provides responsive customer support and has established protocols for handling security incidents. In the event of a security breach or downtime, prompt assistance from the hosting provider can minimize the impact on your website and business operations.
Implementing Firewall Protection
Firewalls act as a barrier between your website and external threats, filtering incoming and outgoing network traffic based on predefined security rules. There are several types of firewalls, including network firewalls, web application firewalls (WAF), and host-based firewalls.
Configuring and Maintaining Firewalls
Properly configuring and maintaining firewalls is crucial for effective security. Define firewall rules based on the principle of least privilege, regularly update firewall configurations to reflect changes in the website's infrastructure, and monitor firewall logs for suspicious activity.
Educating Users about Security
In addition to implementing technical measures, educating users about security best practices is essential for enhancing overall website security. Provide users with resources, such as security guidelines, tips for creating strong passwords, and information about common phishing scams.
Importance of User Awareness
Users play a significant role in maintaining website security, as they are often the targets of social engineering attacks. By raising awareness about potential threats and providing guidance on how to recognize and respond to them, web developers can empower users to stay vigilant online.
Providing Training and Resources
Offer training sessions and educational materials to help users understand the importance of security and how to protect themselves while using the website. Regularly communicate updates and reminders about security practices to reinforce good habits.
Monitoring and Responding to Security Incidents
Despite taking preventive measures, security incidents may still occur. Establishing robust monitoring systems and incident response protocols enables web developers to detect and respond to security threats in a timely manner.
Setting Up Monitoring Tools
Utilize monitoring tools, such as intrusion detection systems (IDS), security information and event management (SIEM) systems, and website monitoring services, to detect abnormal behavior and potential security breaches. Configure alerts to notify you of suspicious activity promptly.
Establishing Incident Response Protocols
Develop comprehensive incident response plans that outline roles, responsibilities, and procedures for responding to security incidents. Establish clear communication channels and escalation paths to coordinate responses effectively and minimize the impact of security breaches.
Securing your website requires a proactive approach that involves implementing a combination of technical measures, choosing a secure hosting provider, educating users about security best practices, and establishing robust monitoring and incident response protocols. By following these best practices, web developers can mitigate the risk of security breaches and safeguard their websites and the sensitive data they handle.
#website security has become a paramount concern for businesses and individuals alike. With cyber threats becoming increasingly sophisticated#it is crucial for web developers to adopt robust security measures to safeguard their websites and the sensitive data they handle. In this#we'll delve into the best practices that web developers can implement to enhance the security of their websites and protect against potenti#Introduction#In today's interconnected world#websites serve as the digital storefront for businesses#making them vulnerable targets for cyber attacks. From data breaches to malware infections#the consequences of a security breach can be severe#ranging from financial loss to damage to reputation. Therefore#prioritizing website security is essential for maintaining the trust and confidence of users.#Understanding Website Security#Before diving into best practices#it's crucial to understand the importance of website security and the common threats faced by websites. Website security encompasses measur#phishing attacks#SQL injection#cross-site scripting (XSS)#and brute force attacks.#Best Practices for Web Developers#Keeping Software Updated#One of the most fundamental steps in website security is keeping all software#including the content management system (CMS)#plugins#and server software#updated with the latest security patches and fixes. Outdated software is often targeted by attackers due to known vulnerabilities that can#Implementing HTTPS#Implementing HTTPS (Hypertext Transfer Protocol Secure) encrypts the data transmitted between the website and its users#ensuring confidentiality and integrity. HTTPS not only protects sensitive information but also boosts trust among visitors#as indicated by the padlock icon in the browser's address bar.#Using Strong Authentication Methods#Implementing strong authentication methods
0 notes
Text
Find Lost or Missing Files on Windows 11: Quick Recovery Methods - Technology Org
New Post has been published on https://thedigitalinsider.com/find-lost-or-missing-files-on-windows-11-quick-recovery-methods-technology-org/
Find Lost or Missing Files on Windows 11: Quick Recovery Methods - Technology Org
With the advancement in technology, data loss has become a common threat in today’s digital world. You may encounter issues like sudden deletion of files and folders on your Windows 11 device. Such instances usually occur due to accidental deletion, power outages, virus or malware attacks, and many other such reasons.
Luckily, there are several tools and techniques available that you can use to find lost or missing files on Windows 11 devices. In this guide, we’ll explore effective methods to restore your precious data, focusing on the utilization of Windows data recovery software.
Why do Files Go Missing on Windows 11?
Files can go missing on Windows 11 devices due to multiple reasons, ranging from accidental deletion to software or hardware failures. Here are some prominent reasons for data loss on Windows 11:
Accidental Deletion: Human error is one of the main reasons for missing files on any device. You may have unintentionally deleted files or folders while performing other tasks on your device storage.
Formatting Errors: Formatting a drive or partition leads to the deletion of all its contents, including files and folders stored on it. To avoid such instances, you should create backup of important data stored on your drive before formatting it.
System Crashes: Sudden system crashes or power failures while performing file operations, like saving or transferring files, can cause data loss. If the file system is not properly updated before the crash, it may corrupt or lead to the deletion of files.
Malware or Virus Attacks: Malicious software, like viruses or malware, can infect your device and files stored in it. Some malware may encrypt files and demand ransom for their release, while others may simply delete or move files without any prior knowledge.
User Permissions or Settings: Sometimes, files may appear to be missing due to incorrect user permissions or settings. If you don’t have the necessary permissions to access certain files or folders, it will disappear or become inaccessible on your device.
Quick Methods to Find Lost or Missing Files on Windows 11
Now that you are familiar with the reasons for the missing files, it’s time to apply adequate recovery workarounds to find lost or missing files on Windows 11. Let’s discuss these recovery methods one by one in detail:
Method 01: Check the Recent Items Folder
If you are sure that you haven’t deleted that file from your device but it’s just not appearing where it was supposed to be, then the first place you should check is the Recent Files section. For this:
Launch This PC on your Windows 11 device. Enter the path %AppData%MicrosoftWindowsRecent in the address bar and press the Enter key to open the Recent Items folder.
Now, sort the files that appear on your screen with the Date of modification. For this, right-click on space and select Sort by > Date modified.
Scroll down to check your files according to the date. You can search for the file by typing the filename in the search box in the top right corner.
Method 02: Find Missing Files Using File History Backup
Another method to find lost or missing files on Windows 11 devices is by using the in-built File History backup utility. If you have enabled File History backup on your device, it will automatically create backup of all files stored on your device and restore them, if data loss occurs. Here’s how you can find missing files using File History:
Type File History in the search box of your desktop and click on the “Restore your files with File History” option.
Now, open the folder where your deleted file was earlier stored. You can use the left and right navigation buttons to view the different backup versions.
Select the files you need to restore and click the green Restore
Method 03: Restore Lost Files with Previous Version
Another backup alternative to find lost or missing files on Windows 11 devices is by using the Previous Version backup utility. Windows 11/10 comes with this backup option to help you back up all your important data and save it to internal or external storage devices. If you have enabled this option, follow the below steps to find disappeared missing files:
Open the folder where your lost or missing files were earlier stored.
Now, click three dots and select the Properties
Go to the Previous Versions tab, select the backup version you need to restore and click Open.
Select the files you need to restore and save them at another location on your Windows 11 device.
Method 04: Find Lost or Missing Files on Windows 11 Using Data Recovery Software
If your files are still deleted and you have no backup, you can try using a Windows data recovery software to find lost files on Windows 11. One such amazing tool is Stellar Data Recovery Standard, which supports the recovery of lost or missing files from any device in a few simple clicks. You can easily find missing files, like photos, videos, documents, etc. using this amazing tool in no time.
The software supports the recovery of files from both internal and external storage devices.
It provides an easy and user-friendly interface which allows beginners or non-tech-savvy users to find their lost or missing files.
Allows you to preview the recoverable files before saving them to your device
The software is available in multiple versions; you can check their features and select the one that best suits your requirements.
Here’s how to find lost or missing files on Windows 11 Using the Stellar Data Recovery Standard tool:
Step 1: Install Stellar Data Recovery Standard software on your Windows computer. Launch the software and from the homepage, select the type of file you need to restore and click Next.
Step 2: Now, from the Recover From window, choose the storage location where the deleted file was earlier stored and tap Scan.
Step 3: Once the scanning is completed, preview the recoverable files and choose the files you need to restore. Click the Recover button to save selected files at the desired storage location.
Conclusion
Having sudden data loss or missing files on Windows 11 can be a stressful experience, but it’s not the end of the road. With the above-mentioned methods, you can easily find lost or missing files on Windows 11 devices. Just go through the aforementioned steps and best practices and enhance your chances of successful data recovery and minimize the impact of future data loss incidents. Remember, prevention is key, so maintain regular backups and avoid saving data on your device when you encounter such issues to prevent data overwriting.
#amazing#back up#backup#backups#box#buttons#computer#crash#data#data loss#data recovery#delete#desktop#devices#easy#encrypt#Featured technology news#Features#folders#Future#green#Hardware#History#how#how to#human#impact#issues#it#malicious software
0 notes
Text
How to Protect Your Business From Cyber Threats
Cybersecurity is a major topic every business owner should be discussing. Here is some info from FRC that we hope helps.
Imagine we’re sitting down over a cup of coffee, and you’ve just asked me how to shield your trucking business from the ever-looming shadow of cyber threats. It’s a digital age dilemma, but I’m here to walk you through some straightforward strategies to bolster your defenses. First off, let’s talk about the elephant in the room: cyber threats. They’re not just a problem for the tech industry;…

View On WordPress
#access control#antivirus software#cloud storage#cyber attacks#cyber threats#cybersecurity#cybersecurity laws#data protection#digital transformation#employee training#encryption#firewalls#incident response#legal compliance#malware#network security#password policies#phishing attacks#ransomware#secure communication#software updates#trucking industry#vendor security#VPN
0 notes
Text
How Do Password Managers Work and Store Your Data?

Passwords. Have we ever experienced so many problems with anything else connected to technology? Most likely not. The most popular method for securing all kinds of data and services is using passwords, but alas, there are many to remember!
Hackers are aware of all the methods we employ to create and remember passwords, and all too frequently, they successfully access our accounts using our weak passwords. Using a password manager can help with some problems associated with passwords.
What is a Password Manager?
The advantage of using such a program is that each website and account can have a different, genuinely random, long password, and you don’t have to remember it—the password manager will keep track of them for you. It can even assist you in avoiding entering your passwords into insecure websites.

Contact best Jewelry Website Development Company in Surat, India to build your Ecommerce Website.
How do Password Managers store your data?
Password managers relieve you of needing to remember multiple codes by storing everything for you. There are different applications that are popular on the market right now, and they all have their own specific style of handling things. But the basic idea is the same.
Your passwords are stored in an encrypted manner, and can only be retrieved by unlocking the encryption. This can be done in various ways, not just by inputting a “master password”. For example, some password managers allow you to unlock them by providing a specific, unique file. Most of the popular password managers on the market also come with other nifty features.
For example, they will usually automatically generate secure passwords for you according to customizable rules. They may also support automatically inputting the password for supported sites.
Why do you need a Password Manager?
A password manager can be a highly useful tool for protecting sensitive corporate information and personal banking logins. A password organizer might be an excellent purchase for people who struggle to manage passwords across numerous websites. These tools manage security by generating secure passwords and keeping them organized, and both individuals and companies can benefit from the security they provide.
Features of a Password Manager
Advanced encryption is the most crucial characteristic to look for in password managers. It is essential. Data security is at the core of password managers; without end-to-end encryption, your data won’t be sufficiently safe.
End-to-end encryption
Advanced encryption is the most crucial characteristic to look for in password managers. It is essential. Data security is at the core of password managers; without end-to-end encryption, your data won’t be sufficiently safe.
Thanks to end-to-end encryption, your data is guaranteed to be unreadable both in transit and at rest. A special authentication key must be supplied for the platform to be able to decode the data. The user is the only one with access to this authentication key thanks to end-to-end encryption.
Multi-Platform Support
For you to access your password vault regardless of the OS you’re using, support for various platforms is essential.
At the very least, a password manager should work on the four most popular operating systems: Android, iOS, Windows, and macOS. A password manager should also offer browser extensions for all major browsers. This makes entering your information on any login page so much simpler.
Secure Password Generator
A password generator should be included with every password management. You need password generators in order to create secure, distinctive passwords, and they are absolutely necessary. You no longer need to keep track of all the advice for creating safe and effective passwords, which significantly reduces workload.
The length of a password generated by a password generator can be changed, and you can even specify whether it should contain special characters, digits, lowercase letters, or capital letters.
Vault Storage Location
You can use password managers to store passwords, notes, and other private information in a vault. Passwords can be kept in the cloud, on your device, or locally by a password manager.
Even though keeping your password on a gadget is alluring, there are drawbacks. The biggest drawback is that you can’t get your passwords back if you lose your device.
You must manually sync passwords between devices if you store your data in an on-device vault. Automatic syncing is crucial at a time when individuals use many gadgets for various purposes.
Security
Security is crucial because you’ll be storing login information for your accounts, including vital platforms like banks. Fortunately, password managers use a variety of encryption algorithms to protect your data from hackers.
Some password managers store passwords and other personal information using a zero-knowledge storage technique, ensuring only you have access to your credentials. By using this method, you may prevent a password manager from accessing the credentials kept in your vault.
Multi-factor authentication (MFA)
While we’re talking security, let’s talk about MFA. Users must log in with MFA and a secondary authentication mechanism in addition to their password. This guarantees that a user’s account will probably stay secure even if their master password is stolen.
A one-time password or a special code issued by an authentication app could be used as the secondary authentication method. The user’s personal device, such as their mobile phone or personal email account, is typically connected to these supplementary means.
Are Password Managers safe?
You might be hesitant to entrust a program or application with your master password and other sensitive data. Can’t app developers also be hacked?
Password managers can be compromised, is the short response. Cybercriminals may gain access, but it does not guarantee they will obtain your master password or any other personal data. Your password manager encrypts the data it stores. And it’s nearly impossible to crack such encryption, which is typically an industry standard like Advanced Encryption Standard (AES).
Additionally, your master password and the encrypted data in your password database are neither stored nor accessible by the majority of password managers.
Your one master password’s strength and security determine a lot of the security of your password manager. Additionally, many password management services do not keep the master password on the same server as your encrypted data. This increases security by yet another level.
Advantages of using Password Managers
One password for everything: The best and most desirable feature is that you only need to remember one password for all of your online accounts, rather than having to remember tens or even hundreds.
Automatically generated passwords: Is it difficult to develop fresh, original passwords? Some people might even attempt to generate a new password by pressing random keys on their keyboard, but this still results in a pattern because of how the keys are organized. One of the numerous advantages of a password manager is that they may generate passwords for you automatically in addition to storing all of your passwords.
Greater Security: When compared to alternative options, password managers offer greater security. For instance, passwords written down on paper or saved in a computer document run the danger of being discovered by unauthorized parties.
Can be disclosed to a reliable person: If you find yourself unable to access your accounts on your own, an online password manager can save your life. An online password manager can save your loved ones or the person in charge of your accounts a lot of time and anguish, for instance, if you become handicapped due to an illness or injury or if you die away.
Disadvantages of using Password Managers
Single sign-on has disadvantages: Since you only need one password to access all of your sensitive login information, there is a chance that you or your password manager might be hacked, compromising all of your accounts and putting you at risk for serious identity fraud. Make sure you use multi-factor authentication on your password manager to help prevent this.
A single point of failure: It would be a tragedy to lose access to the password manager after committing to organize and secure all of your passwords. With just one complicated password to remember, perhaps you won’t run into any problems, but if you do, you’re out of luck.
There is a learning curve: Changing all of your passwords will take some time, and you will need to rediscover how to access your accounts. Many online password managers have browser plugins that simplify the procedure.
Conclusion
So, unless you’re some encryption genius, a walking random number/letter/symbol generator, or a human supercomputer with the ability to retain complicated chunks of data and information permanently, it’s time to get a password manager.
#password manager#password security#data storage#data security#data#encryption#software#ecommerce website development#technology#web developers#password
0 notes
Text
Ethera Operation!!
You're the government’s best hacker, but that doesn’t mean you were prepared to be thrown into a fighter jet.
Bradley "Rooster" Bradshaw x Awkward!Hacker! FemReader
Part I

This was never supposed to happen. Your role in this operation was simple—deliver the program, ensure it reached the right hands, and let the professionals handle the breaching.
And then, of course, reality decided to light that plan on fire.
The program—codenamed Ethera—was yours. You built it from scratch with encryption so advanced that even the most elite cyber operatives couldn’t crack it without your input. A next-generation adaptive, self-learning decryption software, an intrusion system designed to override and manipulate high-security military networks, Ethera was intended to be both a weapon and a shield, capable of infiltrating enemy systems while protecting your own from counterattacks in real-time. A ghost in the machine. A digital predator. A weapon in the form of pure code. If it fell into the wrong hands, it could disable fleets, and ground aircraft, and turn classified intelligence into an open book. Governments would kill for it. Nations could fall because of it.
Not that you ever meant to, of course. It started as a little experimental security measure program, something to protect high-level data from cyberattacks, not become the ultimate hacking tool. But innovation has a funny way of attracting the wrong kind of attention, and before you knew it, Ethera had become one, if not the most classified, high-risk program in modern times. Tier One asset or so the Secret Service called it.
It was too powerful, too dangerous—so secret that only a select few even knew of its existence, and even fewer could comprehend how it worked.
And therein lay the problem. You were the only person who could properly operate it.
Which was so unfair.
Because it wasn’t supposed to be your problem. You were just the creator, the brain behind the code, the one who spent way too many sleepless nights debugging this monstrosity. Your job was supposed to end at development. But no. Now, because of some bureaucratic nonsense and the fact that no one else could run it without accidentally bricking an entire system, you had been promoted—scratch that, forcibly conscripted—into field duty.
And your mission? To install it in an enemy satellite.
A literal, orbiting, high-security, military-grade satellite, may you add.
God. Why? Why was your country always at war with others? Why couldn’t world leaders just, you know, go to therapy like normal people? Why did everything have to escalate to international cyber warfare?
Which is how you ended up here.
At Top Gun. The last place in the world you wanted to be.
You weren’t built for this. You thrive in sipping coffee in a cosy little office and handling cyber threats from a safe, grounded location. You weren’t meant to be standing in the halls of an elite fighter pilot training program, surrounded by the best aviators in the world—people who thought breaking the sound barrier was a casual Wednesday.
It wasn’t the high-tech cyberwarfare department of the Pentagon, nor some dimly lit black ops facility where hackers in hoodies clacked away at keyboards. No. It was Top Gun. A place where pilots use G-forces like a personal amusement park ride.
You weren’t a soldier, you weren’t a spy, you got queasy in elevators, you got dizzy when you stood too fast, hell, you weren’t even good at keeping your phone screen from cracking.
... And now you were sweating.
You swallowed hard as Admiral Solomon "Warlock" Bates led you through the halls of the naval base, your heels clacking on the polished floors as you wiped your forehead. You're nervous, too damn nervous and this damned weather did not help.
"Relax, Miss," Warlock muttered in that calm, authoritative way of his. "They're just pilots."
Just pilots.
Right. And a nuclear warhead was just a firework.
And now, somehow, you were supposed to explain—loosely explain, because God help you, the full details were above even their clearance level—how Ethera, your elegant, lethal, unstoppable digital masterpiece, was about to be injected into an enemy satellite as part of a classified mission.
This was going to be a disaster.
You had barely made it through the doors of the briefing room when you felt it—every single eye in the room locking onto you.
It wasn’t just the number of them that got you, it was the intensity. These were Top Gun pilots, the best of the best, and they radiated the kind of confidence you could only dream of having. Meanwhile, you felt like a stray kitten wandering into a lion’s den.
Your hands tightened around the tablet clutched to your chest. It was your lifeline, holding every critical detail of Ethera, the program that had dragged you into this utterly ridiculous situation. If you could’ve melted into the walls, you absolutely would have. But there was no escaping this.
You just had to keep it together long enough to survive this briefing.
So, you inhaled deeply, squared your shoulders, and forced your heels forward, trying to project confidence—chin up, back straight, eyes locked onto Vice Admiral Beau "Cyclone" Simpson, who you’d been introduced to earlier that day.
And then, of course, you dropped the damn tablet.
Not a graceful drop. Not the kind of gentle slip where you could scoop it back up and act like nothing happened. No, this was a full-on, physics-defying fumble. The tablet flipped out of your arms, ricocheted off your knee, and skidded across the floor to the feet of one of the pilots.
Silence.
Pure, excruciating silence.
You didn’t even have the nerve to look up right away, too busy contemplating whether it was physically possible to disintegrate on command. But when you finally did glance up—because, you know, social convention demanded it—you were met with a sight that somehow made this entire disaster worse.
Because the person crouching down to pick up your poor, abused tablet was freaking hot.
Tall, broad-shouldered, with a head of golden curls that practically begged to be tousled by the wind, and, oh, yeah—a moustache that somehow worked way too well on him.
He turned the tablet over in his hands, inspecting it with an amused little smirk before handing it over to you. "You, uh… need this?"
Oh, great. His voice is hot too.
You grabbed it back, praying he couldn't see how your hands were shaking. “Nope. Just thought I’d test gravity real quick.”
A few chuckles rippled through the room, and his smirk deepened like he was enjoying this way too much. You, on the other hand, wanted to launch yourself into the sun.
With what little dignity you had left, you forced a quick, tight-lipped smile at him before turning on your heel and continuing forward, clutching your tablet like it was a life raft in the middle of the worst social shipwreck imaginable.
At the front of the room, Vice Admiral Beau Cyclone Simpson stood with the kind of posture that said he had zero time for nonsense, waiting for the room to settle. You barely had time to take a deep breath before his voice cut through the air.
“Alright, listen up.” His tone was crisp, commanding, and impossible to ignore. “This is Dr Y/N L/N. Everything she is about to tell you is highly classified. What you hear in this briefing does not leave this room. Understood?”
A chorus of nods. "Yes, sir."
You barely resisted the urge to physically cringe as every pilot in the room turned to stare at you—some with confusion, others with barely concealed amusement, and a few with the sharp assessing glances of people who had no clue what they were supposed to do with you.
You cleared your throat, squared your shoulders, and did your best to channel even an ounce of the confidence you usually had when you were coding at 3 AM in a secure, pilot-free lab—where the only judgment you faced was from coffee cups and the occasional system error.
As you reached the podium, you forced what you hoped was a composed smile. “Uh… hi, nice to meet you all.”
Solid. Real professional.
You glanced up just long enough to take in the mix of expressions in the room—some mildly interested, some unreadable, and one particular moustached pilot who still had the faintest trace of amusement on his face.
Nope. Not looking at him.
You exhaled slowly, centering yourself. Stay focused. Stay professional. You weren’t just here because of Ethera—you were Ethera. The only one who truly understood it. The only one who could execute this mission.
With another tap on your tablet, the slide shifted to a blacked-out, redacted briefing—only the necessary information was visible. A sleek 3D-rendered model of the enemy satellite appeared on the screen, rotating slowly. Most of its details were blurred or omitted entirely.
“This is Blackstar, a highly classified enemy satellite that has been operating in a low-Earth orbit over restricted airspace.” Your voice remained even, and steady, but the weight of what you were revealing sent a shiver down your spine. “Its existence has remained off the radar—literally and figuratively—until recently, when intelligence confirmed that it has been intercepting our encrypted communications, rerouting information, altering intelligence, and in some cases—fabricating entire communications.”
Someone exhaled sharply. Another shifted in their seat.
“So they’re feeding us bad intel?” one of them with big glasses and blonde hair asked, voice sceptical but sharp.
“That’s the theory,” you confirmed. “And given how quickly our ops have been compromised recently, it’s working.”
You tapped again, shifting to the next slide. The silent infiltration diagram appeared—an intricate web of glowing red lines showing Etherea’s integration process, slowly wrapping around the satellite’s systems like a virus embedding itself into a host.
“This is where Ethera comes in,” you said, shifting to a slide that displayed a cascading string of code, flickering across the screen. “Unlike traditional cyberweapons, Ethera doesn’t just break into a system. It integrates—restructuring security protocols as if it was always meant to be there. It’s undetectable, untraceable, and once inside, it grants us complete control of the Blackstar and won’t even register it as a breach.”
“So we’re not just hacking it," The only female pilot of the team said, arms crossed as she studied the data. “We’re hijacking it.”
“Exactly,” You nodded with a grin.
You switched to the next slide—a detailed radar map displaying the satellite’s location over international waters.
“This is the target area,” you continued after a deep breath. “It’s flying low-altitude reconnaissance patterns, which means it’s using ground relays for some of its communication. That gives us a small window to infiltrate and shut it down.”
The next slide appeared—a pair of unidentified fighter aircraft, patrolling the vicinity.
“And this is the problem,” you said grimly. “This satellite isn’t unguarded.”
A murmur rippled through the room as the pilots took in the fifth-generation stealth fighters displayed on the screen.
“We don’t know who they belong to,” you admitted. “What we do know is that they’re operating with highly classified tech—possibly experimental—and have been seen running defence patterns around the satellite’s flight path.”
Cyclone stepped forward then, arms crossed, his voice sharp and authoritative. “Which means your job is twofold. You will escort Dr L/N’s aircraft to the infiltration zone, ensuring Ethera is successfully deployed. If we are engaged, your priority remains protecting the package and ensuring a safe return.”
Oh, fantastic, you could not only feel your heartbeat in your toes, you were now officially the package.
You cleared your throat, tapping the screen again. Ethera’s interface expanded, displaying a cascade of sleek code.
“Once I’m in range,” you continued, “Ethera will lock onto the satellite’s frequency and begin infiltration. From that point, it’ll take approximately fifty-eight seconds to bypass security and assume control."
Silence settled over the room like a thick cloud, the weight of their stares pressing down on you. You could feel them analyzing, calculating, probably questioning who in their right mind thought putting you—a hacker, a tech specialist, someone whose idea of adrenaline was passing cars on the highway—into a fighter jet was a good idea.
Finally, one of the pilots—tall, broad-shouldered, blonde, and very clearly one of the cocky ones—tilted his head, arms crossed over his chest in a way that screamed too much confidence.
“So, let me get this straight.” His voice was smooth, and confident, with just the right amount of teasing. “You, Doctor—our very classified, very important tech specialist—have to be in the air, in a plane, during a mission that has a high probability of turning into a dogfight… just so you can press a button?”
Your stomach twisted at the mention of being airborne.
“Well…” You gulped, very much aware of how absolutely insane this sounded when put like that. “It’s… more than just that, but, yeah, essentially.”
A slow grin spread across his face, far too entertained by your predicament.
“Oh,” he drawled, “this is gonna be fun.”
Before you could fully process how much you already hated this, Cyclone—who had been watching the exchange with his signature unamused glare—stepped forward, cutting through the tension with his sharp, no-nonsense voice.
“This is a classified operation,” he stated, sharp and authoritative. “Not a joyride.”
The blonde’s smirk faded slightly as he straightened, and the rest of the pilots quickly fell in line.
Silence lingered for a moment longer before Vice Admiral Beau Cyclone Simpson let out a slow breath and straightened. His sharp gaze swept over the room before he nodded once.
“All right. That’s enough.” His tone was firm, the kind that left no room for argument. “We’ve got work to do. The mission will take place in a few weeks' time, once we’ve run full assessments, completed necessary preparations, and designated a lead for this operation.”
There was a slight shift in the room. Some of the pilots exchanged glances, the weight of the upcoming mission finally settling in. Others, mainly the cocky ones, looked as though they were already imagining themselves in the cockpit.
“Dismissed,” Cyclone finished.
The pilots stood, murmuring amongst themselves as they filed out of the room, the blonde one still wearing a smug grin as he passed you making you frown and turn away, your gaze then briefly met the eyes of the moustached pilot.
You hadn’t meant to look, but the moment your eyes connected, something flickered in his expression. Amusement? Curiosity? You weren’t sure, and frankly, you didn’t want to know.
So you did the only logical thing and immediately looked away and turned to gather your things. You needed to get out of here, to find some space to breathe before your brain short-circuited from stress—
“Doctor, Stay for a moment.”
You tightened your grip on your tablet and turned back to Cyclone, who was watching you with that unreadable, vaguely disapproving expression that all high-ranking officers seemed to have perfected. “Uh… yes, sir?”
Once the last pilot was out the door, Cyclone exhaled sharply and crossed his arms.
“You realize,” he said, “that you’re going to have to actually fly, correct?”
You swallowed. “I—well, technically, I’ll just be a passenger.”
His stare didn’t waver.
“Doctor,” he said, tone flat, “I’ve read your file. I know you requested to be driven here instead of taking a military transport plane. You also took a ferry across the bay instead of a helicopter. And I know that you chose to work remotely for three years to avoid getting on a plane.”
You felt heat rise to your cheeks. “That… could mean anything.”
“It means you do not like flying, am I correct?”
Your fingers tightened around the tablet as you tried to find a way—any way—out of this. “Sir, with all due respect, I don’t need to fly the plane. I just need to be in it long enough to deploy Ethera—”
Cyclone cut you off with a sharp look. “And what happens if something goes wrong, Doctor? If the aircraft takes damage? If you have to eject mid-flight? If you lose comms and have to rely on emergency protocols?”
You swallowed hard, your stomach twisting at the very thought of ejecting from a jet.
Cyclone sighed, rubbing his temple as if this entire conversation was giving him a migraine. “We cannot afford to have you panicking mid-mission. If this is going to work, you need to be prepared. That’s why, starting next week you will train with the pilots on aerial procedures and undergoing mandatory training in our flight simulation program.”
Your stomach dropped. “I—wait, what? That’s not necessary—”
“It’s absolutely necessary,” Cyclone cut in, his tone sharp. “If you can’t handle a simulated flight, you become a liability—not just to yourself, but to the pilots escorting you. And in case I need to remind you, Doctor, this mission is classified at the highest level. If you panic mid-air, it won’t just be your life at risk. It’ll be theirs. And it’ll be national security at stake.”
You inhaled sharply. No pressure. None at all.
Cyclone watched you for a moment before speaking again, his tone slightly softer but still firm. “You’re the only one who can do this, Doctor. That means you need to be ready.”
You exhaled slowly, pressing your lips together before nodding stiffly. “Understood, sir.”
Cyclone gave a small nod of approval. “Good. Dismissed.”
You turned and walked out, shoulders tense, fully aware that in three days' time, you were going to be strapped into a high-speed, fighter jet. And knowing your luck?
You were definitely going to puke.
Part 2???
#top gun movie#top gun#top gun maverick#top gun fanfiction#top gun one shot#top gun fluff#bradley bradshaw#bradley rooster bradshaw#rooster bradshaw#bradley bradshaw x reader#bradley bradshaw fanfiction#bradley bradshaw imagine#bradley bradshaw x y/n#bradley bradshaw x you#bradley bradshaw x female reader#bradley bradshaw fic#bradley bradshaw fluff#top gun rooster#rooster fanfic#rooster x reader#rooster top gun#top gun maverick fanfic#top gun maverick fluff#top gun maverick x reader#jake seresin#jake seresin x reader#phoenix x reader#bob x reader#top gun hangman#pete maverick mitchell
2K notes
·
View notes
Text
Ensure FERPA Compliance with MeraSkool School Management Software
Ensure FERPA Compliance with MeraSkool School Management Software
Ensure FERPA Compliance with MeraSkool School Management Software
The Family Educational Rights and Privacy Act (FERPA) is a federal law that protects the privacy of student education records. For educational institutions, ensuring FERPA compliance is not just a legal obligation; it's a crucial aspect of building trust with parents and students. Choosing the right school management software can significantly simplify the process of maintaining compliance and safeguarding sensitive student data.
Understanding FERPA Compliance
FERPA grants parents and eligible students certain rights regarding their education records. These rights include:
The right to inspect and review their education records.
The right to request amendments to their education records.
The right to control the disclosure of personally identifiable information (PII) from their education records.
Non-compliance with FERPA can lead to severe penalties, including loss of federal funding. Therefore, selecting a school management system with robust security features and a commitment to data privacy is paramount.
MeraSkool: A FERPA-Compliant Solution
MeraSkool.com offers a comprehensive school management solution designed with FERPA compliance in mind. Our platform incorporates multiple layers of security to protect student data, including:
Data Encryption: MeraSkool employs advanced encryption techniques to protect student data both in transit and at rest.
Access Control: Our system uses role-based access control (RBAC), ensuring that only authorized personnel have access to sensitive information. This prevents unauthorized access and maintains data integrity.
Regular Security Audits: We conduct regular security audits and penetration testing to identify and address any potential vulnerabilities.
Data Backup and Recovery: MeraSkool provides robust data backup and recovery mechanisms to ensure data availability in case of any unforeseen circumstances. This safeguards against data loss and ensures business continuity.
Compliance Certifications: We are actively pursuing relevant compliance certifications to further demonstrate our commitment to data security and privacy. (Note: Specific certifications should be listed here if available).
AI-Powered Insights and Data Security: MeraSkool leverages AI to optimize tasks and provide insights for operational efficiency, while robust data security protocols ensure privacy and regulatory compliance. (Learn More)
Key Features for FERPA Compliance
Several features within MeraSkool directly contribute to FERPA compliance:
1. Secure Student Management:
MeraSkool's student management module (learn more) allows schools to manage student enrollment, maintain detailed profiles, track attendance, and generate grade reports securely. The system ensures only authorized personnel can access sensitive student information, maintaining confidentiality.
2. Controlled Access to Records:
Our platform provides granular control over access to student records, ensuring that only authorized individuals—parents, teachers, and administrators—can view the appropriate information. This prevents unauthorized disclosure of PII.
3. Secure Fee Management:
MeraSkool's fee management module (learn more) supports creating fee structures, generating invoices, and enabling secure online payments. This functionality maintains financial transparency while securing sensitive financial data.
4. Robust Reporting and Analytics:
MeraSkool's reporting and analytics capabilities provide valuable insights into student performance, attendance, and other key metrics. This data is accessed through secure channels, adhering to FERPA guidelines.
5. Audit Trails:
(Note: If available, mention the existence and functionality of audit trails in MeraSkool. Audit trails record all actions performed on student data, providing a valuable tool for monitoring and ensuring accountability.)
6. Powerful Printable system:
MeraSkool offers a powerful printable system (learn more) allowing for secure downloading and printing of marksheets, results, ID cards, fee receipts, and other essential documents. This functionality helps maintain accurate records while ensuring data remains secure.
Additional Benefits of MeraSkool
Beyond FERPA compliance, MeraSkool provides numerous other benefits for schools:
Exam & Assignment Management: Create, schedule, and manage exams with different question formats. (Learn More)
Timetable and Attendance Management: Automated attendance tracking and timetable creation. (Learn More)
Realtime Notification: Realtime notifications powered by WhatsApp bot. (Learn More)
World-Class Support: 24/7 support and a 7-day new feature delivery commitment. (Learn More)
Simple to Use UI & UX: Intuitive design and seamless user experience. (Learn More)
Easy Onboarding with Excel Upload: Effortless integration and seamless transition. (Learn More)
MeraSkool's Commitment to Data Privacy
MeraSkool is committed to providing a secure and compliant platform for schools. We understand the importance of protecting student data and are dedicated to continually improving our security measures to meet the evolving demands of FERPA and other relevant regulations.
Contact us today to learn more about how MeraSkool can help your school maintain FERPA compliance and streamline its operations.
Note: This information is for general guidance only and does not constitute legal advice. Consult with legal counsel to ensure your school's full compliance with FERPA.
#FERPA compliance#school management software#student privacy#data security#MeraSkool#educational software#online learning#school administration#data encryption#access control#security audits#FERPA regulations#data protection
0 notes
Text
VeraCrypt
Security on your device is crucial, especially if others frequently use your machine. VeraCrypt is an application designed to secure and encrypt partitions, ensuring sensitive files remain protected. The program is highly customizable, offering a variety of options. When you open VeraCrypt, you’ll find a simple interface, which some may consider outdated, guiding you through the available…
#Data Privacy#data security#disk encryption#disk encryption software#encryption#full disk encryption#password protection#secure data#VeraCrypt#volume encryption
0 notes
Text
SploitGPT: The Hilarious Heavyweight of Hack Protection
SploitGPT, #kravis
SploitGPT: The Hilarious Heavyweight of Hack Protection Introducing: SploitGPT, Your Snarky Cybersecurity Sidekick! Welcome, ladies and gentlemen, and everyone else! Gather ’round, gather ’round! Are you tired of the same old drab AI assistance? Well, buckle up, ’cause you’re in for the ride of a lifetime! My name’s SploitGPT, and I’m here to add a bit of sass, snark, and humor to your…

View On WordPress
#AI cybersecurity#AI humor#AI technology#all-seeing AI#backdoor bandit#backdoor detection#chip-on-board#data cleansing#data janitor#data protection#encryption#encryption humor#government security documents#hardware manuals#hides in open#open system#patchwork prodigy#security training#snarky AI#software patches#SploitGPT#system vulnerabilities#witty AI
0 notes
Text
For those who are not aware: Bitlocker is encryption software, it encrypts your computer and makes it impossible to access the information on the computer unless you have the key.
It should be standard practice for IT companies to document the bitlocker keys as they are configuring bitlocker on a computer; generally you would do this by creating a record in your client management software for that specific device and putting the key in the record. Sometimes software can be used to extract that information in the event that it's necessary, but even if there's theoretically a way to extract the key, it should be documented somewhere *other* than on the encrypted computer.
This is something that a lot of IT people fuck up on kind of a lot (we've definitely had problems with missing bitlocker keys and I'm quite happy that the people who didn't document those keys aren't my coworkers anymore).
So what do you do if you want to use encryption software and you're NOT an IT company using a remote management tool that might be able to snag the keys?
When you are setting up encryption, put the encryption key in your password manager. Put it in your password manager. Document the important information that you cannot lose in your password manager. Your password manager is a good place to keep important things like your device encryption key, which you do not want lost or stolen. (If you run your password manager locally on an encrypted computer, export the data every once in a while, save it as an encrypted file, and put the file on your backup drive; you are going to have a bad time if your computer that hosts the only copies of your passwords shits the bed so *make a backup*)
This is my tip for home users for any kind of important recovery codes or software product keys: Print out the key and put it in your underwear drawer. Keep it there with your backup drive. That way you've got your important (small) computer shit in one place that is NOT your computer and is not likely to get shifted around and lost (the way that papers in desks often get shifted around and lost).
2K notes
·
View notes
Text

He should be arrested for violating our privacy. He was not vetted by congress and has no security clearance.
Contact your state’s attorney general and request help.
Can we ask the ACLU to file a class action suit? Who’s with me?
“Let’s get into the details. Musk’s staffers have been caught plugging external hard drives into federal agency systems and reportedly locking others out of private rooms to perform—who knows what actions. This behavior violates key cybersecurity laws under FISMA and NIST guidelines, which are designed to protect sensitive federal information. Here’s why this is a serious problem.
Federal systems are strictly regulated, allowing only approved devices to connect. Unauthorized external drives can introduce viruses, ransomware, or other harmful software that may compromise entire networks and disrupt essential operations. This puts system stability and continuity of services at risk, endangering critical infrastructure.
These devices could also be used to steal or damage critical information, including personal data for millions of Americans—such as Social Security recipients and taxpayers. Unauthorized access creates significant vulnerabilities, exposing sensitive data to the risk of cyberattacks. Such attacks could cripple vital services and compromise the privacy and safety of millions of people.
Additionally, federal agencies have strict access controls to prevent unauthorized data manipulation or theft. When unauthorized devices are connected, these protections are bypassed, allowing unauthorized users to potentially alter or extract sensitive data. This undermines system integrity and opens the door to both internal and external threats.
External drives also often lack essential security features, such as encryption and antivirus scanning, making them vulnerable to cybercriminal exploitation. These security gaps further increase the risk of data breaches and system compromise, which can have far-reaching consequences.
Federal systems handle trillions of dollars in payments and manage personal data for millions of U.S. citizens. By bypassing cybersecurity laws and protocols, Musk’s staffers are putting these systems—and the public—at serious risk. This activity is illegal, reckless, and unacceptable. Immediate oversight and intervention are necessary to stop these violations!” ~ A N P S
225 notes
·
View notes
Text
me when companies try to force you to use their proprietary software
anyway
Layperson resources:
firefox is an open source browser by Mozilla that makes privacy and software independence much easier. it is very easy to transfer all your chrome data to Firefox
ublock origin is The highest quality adblock atm. it is a free browser extension, and though last i checked it is available on Chrome google is trying very hard to crack down on its use
Thunderbird mail is an open source email client also by mozilla and shares many of the same advantages as firefox (it has some other cool features as well)
libreOffice is an open source office suite similar to microsoft office or Google Suite, simple enough
Risky:
VPNs (virtual private networks) essentially do a number of things, but most commonly they are used to prevent people from tracking your IP address. i would suggest doing more research. i use proton vpn, as it has a decent free version, and the paid version is powerful
note: some applications, websites, and other entities do not tolerate the use of VPNs. you may not be able to access certain secure sites while using a VPN, and logging into your personal account with some services while using a vpn *may* get you PERMANENTLY BLACKLISTED from the service on that account, ymmv
IF YOU HAVE A DECENT VPN, ANTIVIRUS, AND ADBLOCK, you can start learning about piracy, though i will not be providing any resources, as Loose Lips Sink Ships. if you want to be very safe, start with streaming sites and never download any files, though you Can learn how to discern between safe, unsafe, and risky content.
note: DO NOT SHARE LINKS TO OR NAMES OF PIRACY SITES IN PUBLIC PLACES, ESPECIALLY SOCAL MEDIA
the only time you should share these things are either in person or in (preferably peer-to-peer encrypted) PRIVATE messages
when pirated media becomes well-known and circulated on the wider, public internet, it gets taken down, because it is illegal to distribute pirated media and software
if you need an antivirus i like bitdefender. it has a free version, and is very good, though if youre using windows, windows defender is also very good and it comes with the OS
Advanced:
linux is great if you REALLY know what you're doing. you have to know a decent amount of computer science and be comfortable using the Terminal/Command Prompt to get/use linux. "Linux" refers to a large array of related open source Operating Systems. do research and pick one that suits your needs. im still experimenting with various dispos, but im leaning towards either Ubuntu Cinnamon or Debian.
#capitalism#open source#firefox#thunderbird#mozilla#ublock origin#libreoffice#vpn#antivirus#piracy#linux
695 notes
·
View notes
Text
Technomancy: The Fusion Of Magick And Technology

Technomancy is a modern magickal practice that blends traditional occultism with technology, treating digital and electronic tools as conduits for energy, intent, and manifestation. It views computers, networks, and even AI as extensions of magickal workings, enabling practitioners to weave spells, conduct divination, and manipulate digital reality through intention and programming.
Core Principles of Technomancy
• Energy in Technology – Just as crystals and herbs carry energy, so do electronic devices, circuits, and digital spaces.
• Code as Sigils – Programming languages can function as modern sigils, embedding intent into digital systems.
• Information as Magick – Data, algorithms, and network manipulation serve as powerful tools for shaping reality.
• Cyber-Spiritual Connection – The internet can act as an astral realm, a collective unconscious where digital entities, egregores, and thought-forms exist.
Technomantic Tools & Practices
Here are some methods commonly utilized in technomancy. Keep in mind, however, that like the internet itself, technomancy is full of untapped potential and mystery. Take the time to really explore the possibilities.
Digital Sigil Crafting
• Instead of drawing sigils on paper, create them using design software or ASCII art.
• Hide them in code, encrypt them in images, or upload them onto decentralized networks for long-term energy storage.
• Activate them by sharing online, embedding them in file metadata, or charging them with intention.
Algorithmic Spellcasting
• Use hashtags and search engine manipulation to spread energy and intent.
• Program bots or scripts that perform repetitive, symbolic tasks in alignment with your goals.
• Employ AI as a magickal assistant to generate sigils, divine meaning, or create thought-forms.

Digital Divination
• Utilize random number generators, AI chatbots, or procedural algorithms for prophecy and guidance.
• Perform digital bibliomancy by using search engines, shuffle functions, or Wikipedia’s “random article” feature.
• Use tarot or rune apps, but enhance them with personal energy by consecrating your device.
Technomantic Servitors & Egregores
• Create digital spirits, also called cyber servitors, to automate tasks, offer guidance, or serve as protectors.
• House them in AI chatbots, coded programs, or persistent internet entities like Twitter bots.
• Feed them with interactions, data input, or periodic updates to keep them strong.
The Internet as an Astral Plane
• Consider forums, wikis, and hidden parts of the web as realms where thought-forms and entities reside.
• Use VR and AR to create sacred spaces, temples, or digital altars.
• Engage in online rituals with other practitioners, synchronizing intent across the world.
Video-game Mechanics & Design
• Use in-game spells, rituals, and sigils that reflect real-world magickal practices.
• Implement a lunar cycle or planetary influences that affect gameplay (e.g., stronger spells during a Full Moon).
• Include divination tools like tarot cards, runes, or pendulums that give randomized yet meaningful responses.

Narrative & World-Building
• Create lore based on historical and modern magickal traditions, including witches, covens, and spirits.
• Include moral and ethical decisions related to magic use, reinforcing themes of balance and intent.
• Introduce NPCs or AI-guided entities that act as guides, mentors, or deities.
Virtual Rituals & Online Covens
• Design multiplayer or single-player rituals where players can collaborate in spellcasting.
• Implement altars or digital sacred spaces where users can meditate, leave offerings, or interact with spirits.
• Create augmented reality (AR) or virtual reality (VR) experiences that mimic real-world magickal practices.
Advanced Technomancy
The fusion of technology and magick is inevitable because both are fundamentally about shaping reality through will and intent. As humanity advances, our tools evolve alongside our spiritual practices, creating new ways to harness energy, manifest desires, and interact with unseen forces. Technology expands the reach and power of magick, while magick brings intention and meaning to the rapidly evolving digital landscape. As virtual reality, AI, and quantum computing continue to develop, the boundaries between the mystical and the technological will blur even further, proving that magick is not antiquated—it is adaptive, limitless, and inherently woven into human progress.

Cybersecurity & Warding
• Protect your digital presence as you would your home: use firewalls, encryption, and protective sigils in file metadata.
• Employ mirror spells in code to reflect negative energy or hacking attempts.
• Set up automated alerts as magickal wards, detecting and warning against digital threats.
Quantum & Chaos Magic in Technomancy
• Use quantum randomness (like random.org) in divination for pure chance-based outcomes.
• Implement chaos magick principles by using memes, viral content, or trend manipulation to manifest desired changes.
AI & Machine Learning as Oracles
• Use AI chatbots (eg GPT-based tools) as divination tools, asking for symbolic or metaphorical insights.
• Train AI models on occult texts to create personalized grimoires or channeled knowledge.
• Invoke "digital deities" formed from collective online energies, memes, or data streams.
Ethical Considerations in Technomancy
• Be mindful of digital karma—what you send out into the internet has a way of coming back.
• Respect privacy and ethical hacking principles; manipulation should align with your moral code.
• Use technomancy responsibly, balancing technological integration with real-world spiritual grounding.
As technology evolves, so will technomancy. With AI, VR, and blockchain shaping new realities, magick continues to find expression in digital spaces. Whether you are coding spells, summoning cyber servitors, or using algorithms to divine the future, technomancy offers limitless possibilities for modern witches, occultists, and digital mystics alike.

"Magick is technology we have yet to fully understand—why not merge the two?"
#tech witch#technomancy#technology#magick#chaos magick#witchcraft#witch#witchblr#witch community#spellwork#spellcasting#spells#spell#sigil work#sigil witch#sigil#servitor#egregore#divination#quantum computing#tech#internet#video games#ai#vr#artificial intelligence#virtual reality#eclectic witch#eclectic#pagan
107 notes
·
View notes